Mollitiam Industries, a relatively obscure Spanish developer of spyware, is set to close its doors.
The news of the company’s closure was initially highlighted by the intelligence and surveillance news platform Intelligence Online, which attributed the failure to financial difficulties. Public business records verify that Mollitiam filed for bankruptcy on January 23.
Unlike more prominent companies in the field such as Hacking Team, NSO Group, and Paragon Solutions, Mollitiam Industries has largely operated behind the scenes. This obscurity is partly due to the nature of the spyware sector, where numerous vendors prefer to avoid the limelight.
However, Mollitiam’s low profile may also stem from being based in Spain, a region that garners limited attention from international English-language media. Furthermore, the company was primarily associated with a solitary scandal in Colombia, another area frequently underreported in English-speaking outlets.
As of this writing, Mollitiam Industries’ official website remains operational. Attempts to reach the company via the email address listed on their site went unanswered. When TechCrunch tried calling the phone number found on the company’s Google Maps listing, the line was busy. According to its official LinkedIn page, Mollitiam Industries employed between 11 and 50 people.
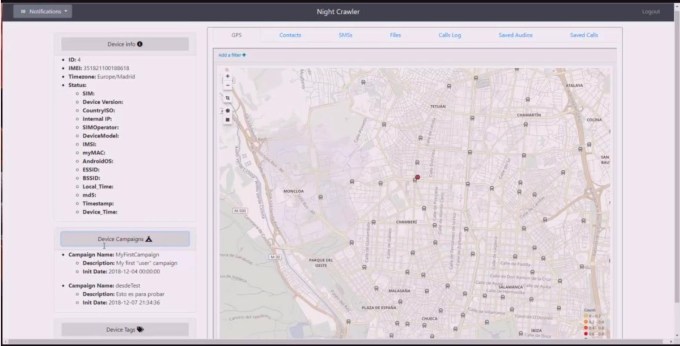
In 2021, Mollitiam Industries first gained mainstream media attention. Wired reported that a brochure accidentally exposed online by a third party revealed the startup’s development of spyware named Invisible Man and Night Crawler, tools designed to covertly extract information from targeted devices, including data from messaging applications like Telegram and WhatsApp, as well as activating cameras and microphones, stealing passwords, and logging keystrokes.
The previous year, in 2020, Colombian news outlet Semana disclosed that its reporters and premises had been subject to both physical and digital surveillance by the nation’s military intelligence, who allegedly threatened the journalists with intimidation tactics, including sending them tombstones. This surveillance followed the magazine’s investigations into military misconduct in 2019.
“A colonel in cyber intelligence offered me 50 million pesos [about $15,000 at that time] to deploy malware on the computers of Semana journalists to access their information,” a source informed the magazine.
Contact Us
If you possess additional information about Mollitiam Industries or other spyware developers, please reach out to Lorenzo Franceschi-Bicchierai securely on Signal at +1 917 257 1382, or via Telegram and Keybase @lorenzofb, or through email. You can also reach TechCrunch via SecureDrop.
It appears that the malware was developed by Mollitiam Industries, as suggested by a contract image between the company and the National Army of Colombia.
This contract indicated that the military offered nearly 3 billion pesos (around $900,000 at the time) to procure a system known as “Hombre Invisible” (or Invisible Man). The software was allegedly capable of infecting macOS and Windows devices remotely by concealing itself within Office documents or through USB drives. The malware was reported to bypass antivirus protections and enable military officials to target an “unlimited” number of active devices.
“This tool gives us full access: we can infiltrate any computer, gather information from WhatsApp and Telegram Web calls and conversations, retrieve archived or deleted messages, photos, and generally anything stored in the memory of the infected device,” said an anonymous informant to Semana.
In the same year that the Colombia scandal broke, Mollitiam Industries participated in an online conference organized by ISS World, aimed at firms intending to provide products for law enforcement and intelligence services.
During this conference, the company noted that increased end-to-end encryption was hindering their ability to conduct surveillance and discussed the necessity of employing malware to compromise target devices to gain access to communications. The event description stated, “Mollitiam will detail the origins of this strategy through software demonstrations and share innovative features such as the capability to record WhatsApp VoIP calls.”
Mollitiam Industries was reportedly still operational at least until late 2023, according to Meta. In early 2024, Meta released a report detailing the removal of a network of fake accounts on Facebook and Instagram linked to Mollitiam Industries.
“Mollitiam Industries and its clients operated fake accounts to test their malicious capabilities on their own accounts and to scrape public information. Similar to other surveillance firms, they used IP-logging links to track their targets’ IP addresses,” the report explained. “They also engaged in phishing and social engineering strategies primarily targeting individuals in Spain, Colombia, and Peru, including political opposition members, journalists, anti-corruption advocates, and activists opposing police misconduct.”
Recently, Spain, especially Barcelona, has emerged as a center for spyware startups, many established by foreigners who are enlisting security researchers from other countries such as Italy and Israel.
Despite receiving minimal attention, Mollitiam’s activities were monitored by Amnesty International. Jurre van Bergen, a technologist at Amnesty International’s Security Lab, told TechCrunch that his team discovered Mollitiam Industries’ Windows samples and identified a command and control server listed on Censys—a search engine for internet-connected devices—dubbed “Invisible Man Login,” clearly referencing one of the company’s offerings.
“It’s extremely negligent for a spyware manufacturer to fail to secure that behind a firewall,” van Bergen remarked to TechCrunch. “Given their evident carelessness, their bankruptcy doesn’t come as a shock.”
Compiled by Techarena.au.
Fanpage: TechArena.au
Watch more about AI – Artificial Intelligence


