A security breach at the mobile tracking service mSpy has compromised the confidentiality of millions of users who purchased its cellphone monitoring software in the last ten years, including the details of the Ukraine-based organization that owns it.
In May 2024, unidentified hackers appropriated millions of customer service records from mSpy, encompassing sensitive personal data, email correspondences with support, and various attachments that include private documents. The intrusion into spyware suppliers like mSpy is increasingly frequent, yet it’s especially concerning due to the nature of the private information involved, affecting the individuals who sought the service.
The breach impacted customer service logs going back to 2014, extracted from the company’s customer support system powered by Zendesk.
mSpy markets itself as a tool for parents to monitor their children or for employers to supervise employees, yet it’s commonly utilized for spying on individuals without their consent, earning it the label “stalkerware.”
The mSpy application enables the installer, usually someone with prior physical access to the target’s phone, to clandestinely observe the device’s activity in live time.
mSpy’s clientele records, as per an analysis by TechCrunch – obtained independently, include communications from individuals aiming to stealthily track the devices of spouses, relatives, or offspring. These communications include customer support inquiries from high-ranking officials in the U.S. military, a judge from a U.S. federal appeals court, a governmental watchdog, and a sheriff’s department in Arkansas seeking a complimentary trial of the software.
Despite millions of customer service tickets being leaked, they likely represent only a fraction of mSpy’s overall clientele, suggesting a significantly wider user base.
Over a month subsequent to the breach, its owners, Brainstack, a company based in Ukraine, have neither recognized nor publicly disclosed the incident.
Data breach notification expert Troy Hunt, the creator of Have I Been Pwned, acquired the exhaustive leaked dataset, incorporating approximately 2.4 million unique customer email addresses into the database of previous breaches on his platform.
Hunt confirmed the accuracy of the leaked data after reaching out to several subscribers of Have I Been Pwned who were affected.
This incident marks mSpy as the latest phone surveillance operation to suffer a cyberattack, echoing the vulnerability of spyware vendors in safeguarding their data—whether it belongs to their clientele or their surveillance targets.
An Analysis of mSpy Customer Correspondences
By examining over 100 gigabytes of Zendesk data, TechCrunch revealed millions of individualized customer service tickets, including associated email addresses and detailed correspondences.
Among these were emails from individuals unaware they were being targeted by mSpy users. The compilation also documented instances of journalists seeking comments from mSpy following a past data breach in 2018. Additionally, it encompassed efforts by U.S. law enforcement to issue subpoenas and legal orders to mSpy. In one instance, an FBI agent received billing and address information about an mSpy user – a suspect in a kidnapping and murder case – after a brief interaction via email.
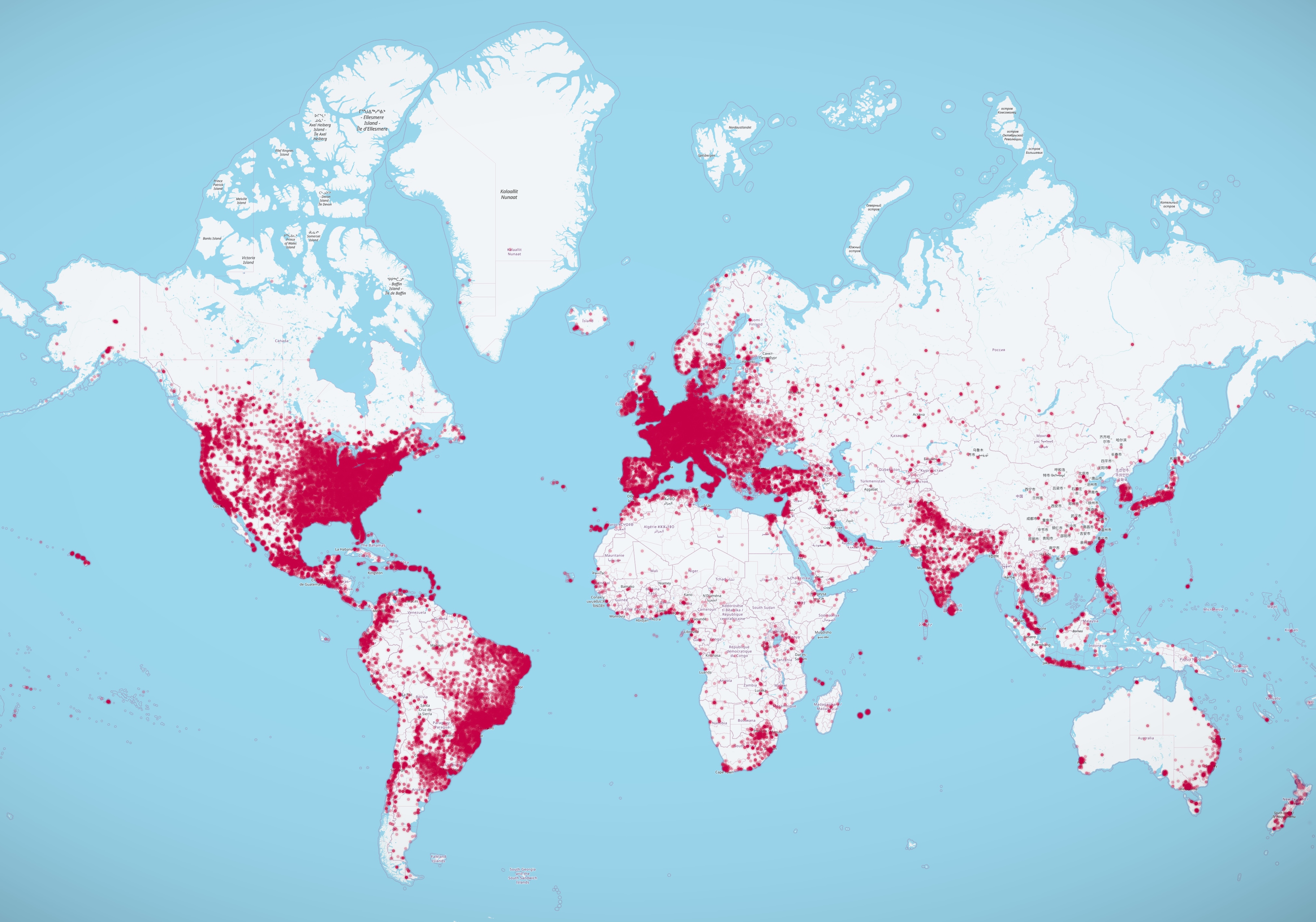
The customer tickets offered insights into mSpy users, including their approximate locations discerned from the IP address linked to the sender’s device.
Mapping these locations displayed a global distribution of mSpy’s clientele, spotlighting significant concentrations in Europe, India, Japan, South America, the UK, and the US.
While purchasing spyware is not illegal per se, its sale or use for unauthorized espionage breaks the law. In the past, U.S. authorities have proceeded against spyware vendors, and those deploying such software unlawfully risk facing legal repercussions for infringing upon wiretapping regulations.
The disclosed emails cast mSpy and its administrators in full awareness of the software’s utilization for unauthorized monitoring, highlighted by user inquiries on how to remove mSpy after discovery by a spouse. Furthermore, the involvement of U.S. governmental organizations, police entities, and the judiciary raises questions about legal compliance in using such surveillance tools.
Of particular note, one email request for a refund detected in the dataset belonged to Kevin Newsom, an appellate judge for the U.S. Court of Appeals for the Eleventh Circuit, who conducted correspondence using his official government email.
Kate Adams from the U.S. Court of Appeals for the Eleventh Circuit clarified that Judge Newsom employed mSpy strictly for personal matters pertaining to his family. Adams refrained from commenting further on Newsom’s usage or if it was consensual.
The dataset captured mSpy’s appeal among U.S. authorities and law enforcement endeavors. A query from an employee at the Office of the Inspector General for the Social Security Administration explored the potential application of mSpy in criminal investigations, without elaborating on specifics.
Contact attempts to the Social Security Administration’s inspector general’s office for comments on the inquiry remained unanswered.
Additionally, a request for mSpy free trials came from the Arkansas County sheriff’s department, aiming to demonstrate the software’s capabilities to local parents. The officer in question did not respond to inquiries regarding the nature of his communication with mSpy.
Unveiling mSpy’s Operator
The recent breach is the third of its kind since mSpy’s inception around 2010, indicating substantial data accumulation due to its longevity in the spyware market.
Despite its significant footprint, mSpy’s operators have managed to stay under the radar, largely avoiding the consequences associated with running an globally operational surveillance enterprise, which is deemed illegal across numerous jurisdictions.
The exposure of mSpy’s parent company, a Ukrainian technology firm named Brainstack, came to light through this data breach.
Although Brainstack’s public representations skirt any direct association with mSpy, preferring instead to label its involvement as related to a “parental control” app, the leaked data undeniably ties the company to mSpy’s extensive operations.
Analysis of the Zendesk data revealed numerous Brainstack employees, participating in customer support tasks for mSpy, pointing to a deep level of involvement in its day-to-day functions.
Upon reaching out, two Brainstack workers verified their identities as seen in the leaked data but refrained from discussing their roles at the company.
Despite repeated attempts for a response, Brainstack’s top executives, including CEO Volodymyr Sitnikov and executive Kateryna Yurchuk, remained silent. A representative, opting to remain unnamed, refrained from questioning our findings but did not furnish further details regarding executive inquiries.
The exact method of the Zendesk breach and the perpetrator(s) remain unidentified. The violation came to public awareness through the disclosure by Swiss hacker maia arson crimew, with the compromised data later shared with DDoSecrets, a non-profit organization aimed at facilitating the release of leaked information for public interest.
Zendesk spokesperson Courtney Blake stated to TechCrunch that, as of current, there is no evidence to suggest a compromise of Zendesk’s infrastructure. Blake did not comment on the compatibility of mSpy’s Zendesk usage with the platform’s service terms.
“We remain dedicated to enforcing our User Content and Conduct Policy, and will investigate any alleged violations rigorously, in line with our procedural guidelines,” the spokesperson remarked.
For those in need of assistance, the National Domestic Violence Hotline (1-800-799-7233) offers round-the-clock, confidential support to individuals impacted by domestic abuse and violence. In urgent situations, dial 911. Resources for those suspecting their device has been compromised by spyware are available at the Coalition Against Stalkerware.
Compiled by Techarena.au.
Fanpage: TechArena.au
Watch more about AI – Artificial Intelligence