A cyber intrusion and data leak involving the location data firm Gravy Analytics poses a significant risk to the privacy of millions globally, as many smartphone applications have inadvertently disclosed sensitive location information collected by the company.
While the complete extent of the data breach remains unclear, the hacker has already exposed a substantial amount of location data from leading consumer mobile applications — including fitness and health, dating, transit apps, and well-known gaming platforms. This data reflects countless location points indicating where individuals reside, work, and travel.
Reports of the breach surfaced last weekend when a hacker shared screenshots of the location data on a Russian-language cybercrime forum, claiming to have stolen several terabytes of consumer information from Gravy Analytics. Independent news outlet 404 Media was the first to cover the forum post detailing the apparent data breach, which allegedly includes historical location information from millions of smartphones.
Norway’s NRK reported on January 11 that Unacast, the parent corporation of Gravy Analytics, notified the country’s data protection authorities about the breach, as mandated by law.
Unacast was established in Norway in 2004 and merged with Gravy Analytics in 2023 to create what it claimed to be one of the largest collections of consumer location data. Gravy Analytics asserts that it monitors over a billion devices daily around the globe.
In a data breach notification submitted in Norway, Unacast reported that it discovered on January 4 that a hacker had accessed files from its Amazon cloud storage using a “misappropriated key.” The company indicated that it learned of the breach through communication with the hacker but did not provide further information. Following the incident, the firm temporarily suspended its operations.
Unacast informed in its notice that it also alerted UK data protection authorities about the incident. Lucy Milburn, a representative for the UK’s Information Commissioner’s Office, confirmed to TechCrunch that the ICO has “received a report from Gravy Analytics and is conducting inquiries.”
Executives Jeff White and Thomas Walle from Unacast did not respond to multiple email inquiries from TechCrunch this week. In a statement sent to TechCrunch from a generic Gravy Analytics email account over the weekend, Unacast confirmed the breach, stating that its “investigation remains ongoing.”
At the time of writing, Gravy Analytics’ website was still down, and several connected domains appeared to be non-operational based on TechCrunch’s checks over the previous week.
30 Million Location Data Points Compromised
Data privacy advocates have consistently warned about the threats posed to individual privacy and national security by data brokers. Researchers who accessed the sample of Gravy Analytics’ location data leaked by the hacker report that this information has the potential to comprehensively track people’s recent movements.
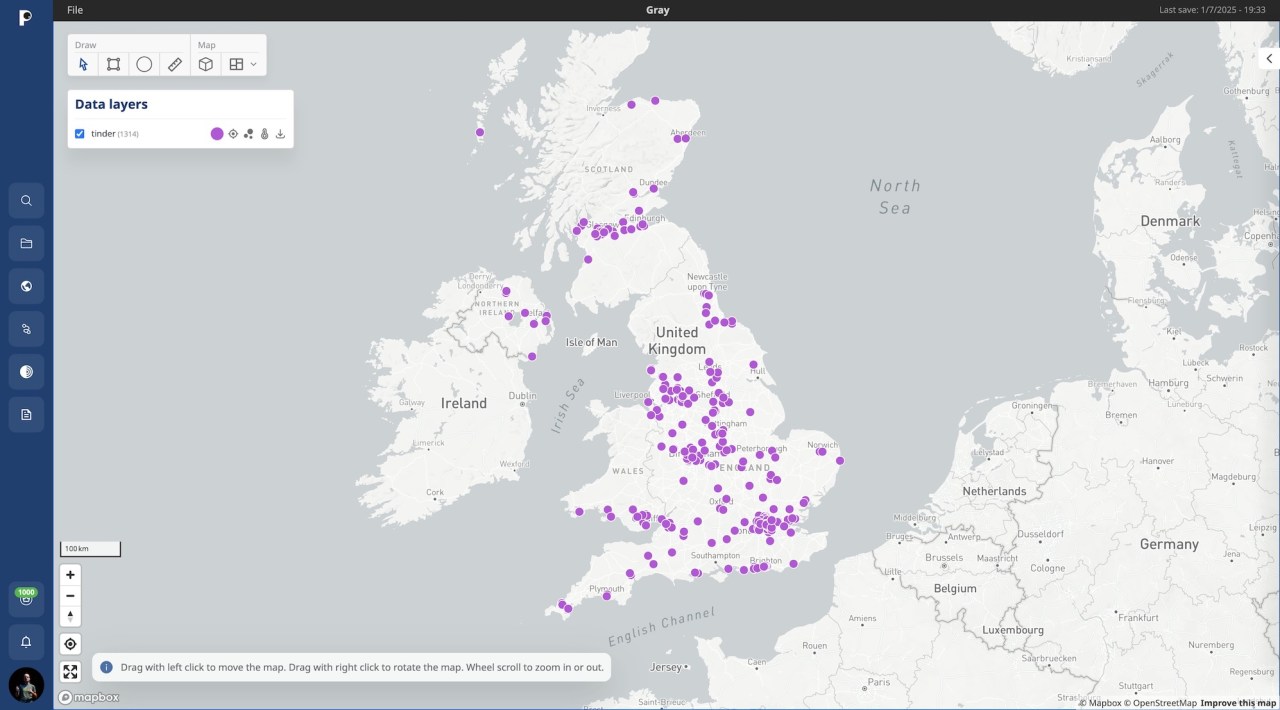
Baptiste Robert, CEO of digital security company Predicta Lab, who acquired a copy of the leaked dataset, mentioned in a post on X that the dataset contained upwards of 30 million location data points. These points represented devices present at significant locations such as The White House in Washington, D.C.; the Kremlin in Moscow; Vatican City; and military installations around the globe. One map shared by Robert illustrated the location data of Tinder users across the United Kingdom. Additionally, another post demonstrated how it is possible to identify individuals likely serving in the military by overlaying the extracted location data with known Russian military facility positions.
Robert cautioned that the data facilitates the easy identification of average individuals; one case tracked a person from New York to their residence in Tennessee. Forbes reported the concerning risks this dataset presents for LGBTQ+ individuals, whose app-derived location data could expose them in regions where homosexuality is criminalized.
Announcement of the breach follows the Federal Trade Commission’s decision to prohibit Gravy Analytics and its subsidiary Venntel from collecting and selling Americans’ location data without explicit consumer consent. The FTC accused the company of illicitly tracking individuals to delicate locations, such as medical facilities and military bases.
Location Data Extracted from Advertising Networks
Gravy Analytics accumulates much of its location data through real-time bidding, an essential aspect of the online advertisement sector, which determines, within a fraction of a second, which advertiser gets to serve an ad to your device.
During this rapid auction, participating advertisers can access certain device information, such as the manufacturer and model, IP addresses (which indicate approximate locations), and occasionally more precise location data granted by the app user, alongside other technical details that influence which ad is displayed.
However, this mechanism also allows any bidding advertiser — or those monitoring the auctions — to tap into a wealth of “bidstream” data comprising device particulars. Data brokers, including those servicing governmental entities, can merge this gathered information with other data to create a comprehensive profile of individuals’ lives and movements.
Security researchers, including Predicta Lab’s Robert, have analyzed location data revealing thousands of advertising applications that shared, often unknowingly, bidstream information with data brokers.
The dataset comprises data sourced from widely used Android and iPhone applications, such as FlightRadar, Grindr, and Tinder — all of which have denied any direct partnerships with Gravy Analytics but admitted to displaying advertisements. However, due to the nature of the advertising industry, ad-serving applications can have their users’ data collected without their explicit knowledge or consent.
As noted by 404 Media, the method Gravy Analytics uses to gather its extensive location data is unclear, including whether the data was collected directly or sourced from other brokers. 404 Media found that a considerable portion of the location data was inferred using the device owner’s IP address, which can be geolocated for estimating their real-world position, rather than relying on the user permitting the app to access GPS coordinates.
Steps to Mitigate Ad Surveillance
According to the Electronic Frontier Foundation, ad auctions are prevalent across nearly all websites, but individuals can take several precautions to protect themselves from advertising surveillance.
Utilizing an ad-blocker or a mobile content blocker can significantly aid in preventing ad surveillance by blocking the ad code from loading on the user’s browser altogether.
Both Android devices and iPhones come equipped with built-in features that complicate advertisers’ ability to track individual users across different applications or the web, linking their anonymous device data to their real-world identities. The EFF also provides an informative guide to inspect these device settings.
For Apple users, navigating to the “Tracking” settings in your device will allow you to disable app tracking requests. This action effectively zeros out your device’s unique identifier, making it indistinguishable from others.
“By disabling the app tracking, your data will not be shared,” Robert stated in an interview with TechCrunch.
Android users should access their phone settings under “Privacy” and then “Ads.” If available, you have the option to delete your advertising ID to prevent access by applications to your unique identifier in future. For those without this setting, routinely resetting advertising IDs is still advisable.
Limiting applications from accessing your precise location when it is not necessary will further reduce your data exposure.
Updated with comments from the ICO.
Contact Zack Whittaker securely on Signal and WhatsApp at +1 646-755-8849. You can also share documents securely with TechCrunch via SecureDrop.
Compiled by Techarena.au.
Fanpage: TechArena.au
Watch more about AI – Artificial Intelligence


