In the wake of the Port of Seattle disclosing a “potential” cyberattack on its infrastructure, operations at Seattle-Tacoma Airport have been severely disrupted, remaining mostly offline and plunging travelers into turmoil. This situation serves as a stark reminder of the importance of robust cybersecurity measures. Learn more about the incident from my experience.
Thankfully, the cyber intrusion hasn’t led to catastrophic outcomes such as aircraft mishaps or scheduling conflicts on runways, thanks to the stringent security protocols enforced by federal aviation authorities.
What we’re witnessing instead is a cautionary tale about the perils of cybersecurity complacency, with no clear end in sight as officials have yet to announce when systems will be fully restored.
My personal realization of the severity came on Sunday. Attempting to utilize the SEA Spot Saver for a faster security check-in – a lesser-known but incredibly efficient service – I was met with an error message indicative of significant underlying issues. Had I kept up with news from my own outlet over the weekend, I would have understood this as a symptom of a compromised DNS setup within the Port’s internet architecture. (Although, the Spot Saver service is temporarily being operated by Clear.)
Fortuitously, I was traveling light and encountered minimal security delays, possibly due to traffic issues on the interstate.
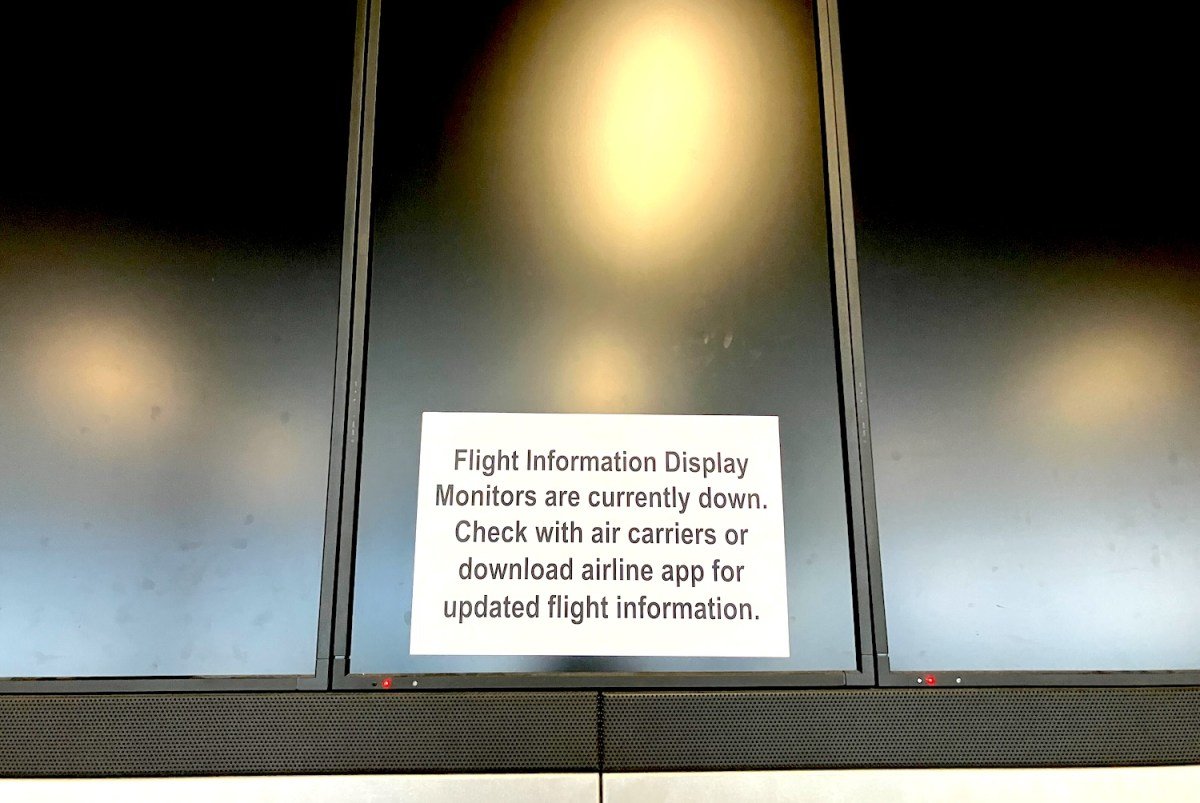
Upon arrival, it became evident that something was amiss. Screens normally showcasing flight details were dark, attributing it initially to ongoing construction activities instead of a cyber event.
It wasn’t until reaching the “S” concourse that the full impact was undeniable. Every display was turned off, including TV monitors and agent screens, making it impossible to verify flight details.
Consultation with gate agents confirmed my flight but also revealed a broader system failure affecting shared airport operations. Despite these challenges, agents were making do, sidelining luggage policies and struggling with internal communications.
Agents appeared to manage with a largely inoperative system, affecting various airlines sharing the “S” concourse. Announcements were made over the PA system due to the inability to display information digitally. Perry Cooper, a spokesperson for Sea-Tac, later indicated that my experience wasn’t reflective of the entire airport’s conditions.
Check-in kiosks were operational but with limited functionality, dashing any hopes of a surprise upgrade in my case.
The reliance on paper tickets and manual processes which might seem outdated, proved to be a fallback for some, though not without its share of confusion and misdirection.
Agents and makeshift signs nudged passengers towards the airport app as a workaround, highlighting the vulnerability of such digital solutions to cyber threats.
The incident raises questions about the vulnerability of various airport systems to a single attack, underscoring a lack of resilience and the importance of segregating critical operations from one another.
This experience wasn’t just about the inconvenience but shed light on broader issues within government-managed IT infrastructure, suggesting a need for substantial improvements to ensure the robustness of critical systems such as airports.
The incident at Sea-Tac underscores the growing threat of cyberattacks against public infrastructure, including those by ransomware and AI-driven phishing scams. With such attacks on the rise, preventive measures are crucial.
Travelers passing through Sea-Tac are advised to allocate extra time and download necessary apps for updates, as local governments work to manage the situation. For ongoing updates, visitors can check the crisis page.
Compiled by Techarena.au.
Fanpage: TechArena.au
Watch more about AI – Artificial Intelligence