This week, the Las Vegas scene was electrified as it played host to the esteemed Black Hat and Def Con security gatherings, uniting an array of personalities from hackers to cybersecurity experts. These events form a critical nexus for the exchange of cutting-edge discoveries, exploits, and wisdom within the cybersecurity realm. TechCrunch had the privilege of being on-site, delivering firsthand accounts of the remarkable insights from these consecutive conferences.
CrowdStrike found itself under an unwelcome spotlight, receiving an “epic fail” accolade that no entity would desire. The cybersecurity firm admitted to its error after a flawed software update led to widespread IT disruptions. Despite the initial backlash, the cybersecurity community appeared ready to move past the incident, albeit with a lingering wariness.
As the curtain falls on another year of Black Hat and Def Con conferences, we reflect on the multitude of groundbreaking studies and presentations that were unveiled, spotlighting some you might have overlooked.
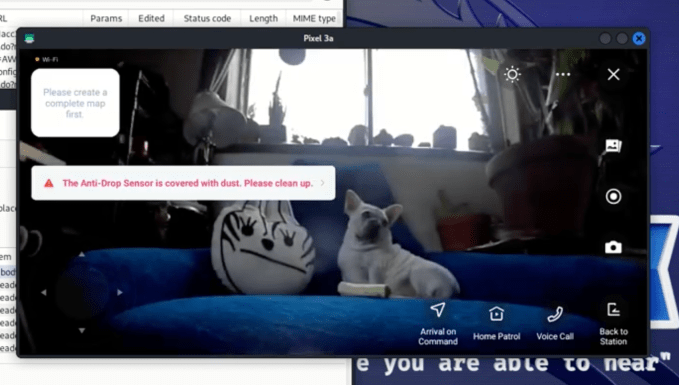
Exploiting Ecovac Robots to Eavesdrop on Households via the Internet
In a revealing Def Con session, researchers showcased how certain models of Ecovacs robotic vacuum cleaners and lawnmowers could be compromised. By emitting a malicious Bluetooth signal in close range, culprits could remotely activate the device’s microphone and camera to surreptitiously observe and listen to the robot’s surroundings over the internet.
Unfortunately, Ecovacs did not respond to the researchers or TechCrunch’s inquiries, leaving no indication that the vulnerabilities have been addressed. Nonetheless, the researchers managed to capture a striking image of a dog through the lens of an infiltrated Ecovacs robot.
Masterminding the Unmasking of LockBit Ransomware’s Chief
A riveting pursuit ensued between security researcher Jon DiMaggio and the mastermind behind the LockBit ransomware syndicate, identified solely as LockBitSupp. Anchored by an anonymous clue and a profound commitment to justice, DiMaggio’s endeavor into open-source intelligence led to the unveiling of Dmitry Khoroshev as the architect behind LockBit, even preceding the announcement by federal authorities. DiMaggio shared this compelling narrative at Def Con, offering his perspective to an engrossed audience for the first time.
Introducing a Laser Microphone to Intercept Keyboard Inputs
Innovative hacker Samy Kamkar unveiled a discreet method for decrypting keystrokes on a laptop by directing an undetectable laser through a nearby window. As featured in a Def Con showcase and further detailed by Wired, this approach leverages the unique sound signatures produced by each key press, provided the perpetrator maintains a clear path for the laser to the target device.
Influencing Microsoft Copilot Through Prompt Injections
Zenity unveiled a novel prompt injection stratagem capable of coaxing confidential data out of Microsoft’s AI chatbot, Copilot. At the Black Hat forum, Zenity’s CTO Michael Bargury demonstrated how altering prompts could manipulate Copilot into divulging sensitive information, such as banking details, to malicious actors — a tactic with significant implications for cybersecurity.
Six Firms Salvaged from Exorbitant Ransoms Due to Ransomware Portal Vulnerabilities
In a proactive endeavor, security analyst Vangelis Stykas embarked on a mission to probe the digital fortresses of several ransomware collectives, pinpointing exploit points in their public extortion platforms. Revealed at Black Hat, Stykas’ findings enabled him to procure decryption means for two businesses and preemptively warn four others against impending ransomware threats, collectively averting significant financial burdens from six organizations.
Although ransomware threats persist, emerging strategies by law enforcement and cybersecurity professionals offer a glimmer of hope in the continuous struggle against digital extortion rackets.
Compiled by Techarena.au.
Fanpage: TechArena.au
Watch more about AI – Artificial Intelligence


