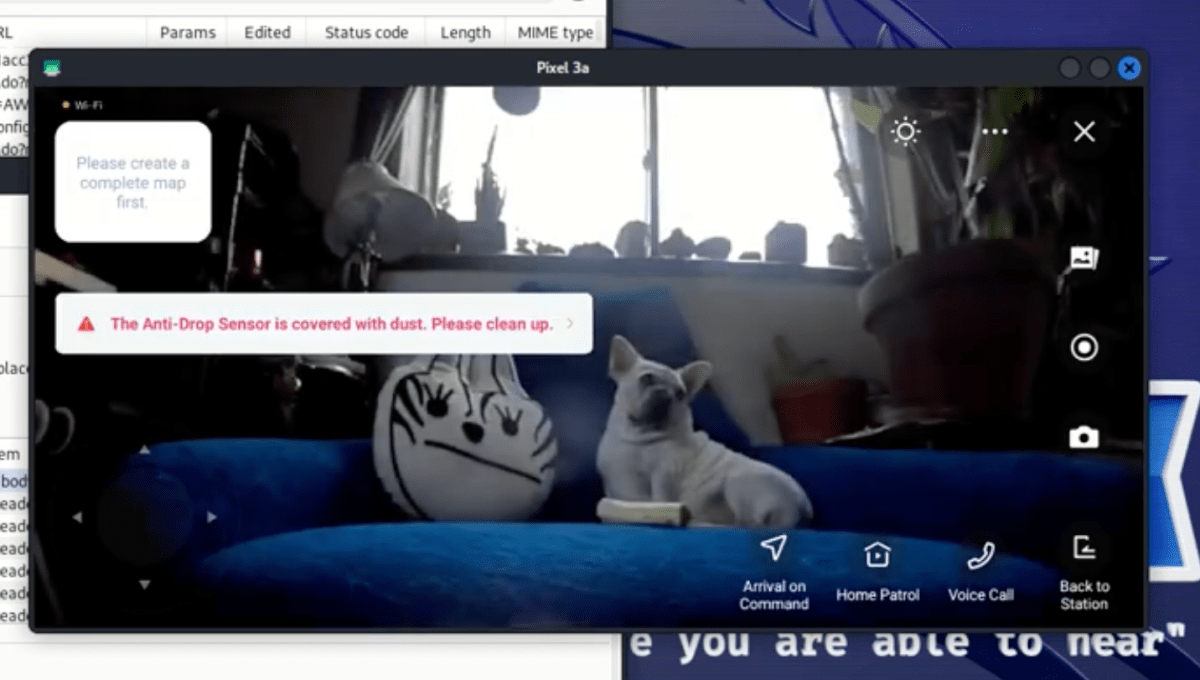
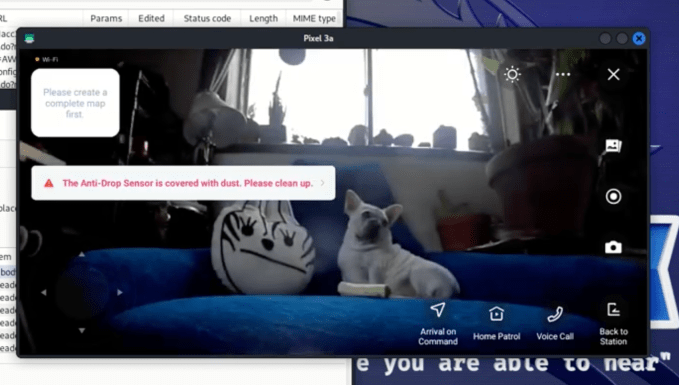
Recent investigations have discovered that cyber attackers can hijack robotic vacuum cleaners and lawn mowers produced by Ecovacs, enabling them to clandestinely observe homeowners through the gadgets’ built-in cameras and microphones.
At the upcoming Def Con hacking event this Saturday, security analysts Dennis Giese and Braelynn will present their findings on vulnerabilities within Ecovacs’ robotic devices. Their examination revealed several security loopholes that allow malefactors to connect to these robots using Bluetooth, turning on their microphones and cameras without detection.
“The level of security was exceptionally poor,” Giese shared with TechCrunch in a pre-conference discussion.
After identifying these flaws, the duo reached out to Ecovacs, but their concerns went unanswered, suggesting that these security gaps remain open and susceptible to exploitation.
Requests for comment from Ecovacs have remained unanswered by the company, as reported by TechCrunch.
A critical issue pinpointed by the researchers is the ability for anyone within a 450 feet radius (roughly 130 meters) to hijack an Ecovacs device through Bluetooth using just a smartphone. Once in control, attackers can remotely commandeer the device since these robots connect through Wi-Fi to the internet.
“By sending a quickly executed payload, it establishes a connection back to our system. This could be a server located anywhere on the internet, giving us remote control of the robot,” Giese explained. “We could access Wi-Fi credentials, retrieve saved maps, and since we’re operating within the robot’s Linux system, we can tap into cameras, microphones, you name it.”
Giese revealed that the Bluetooth function remains constantly active on the lawn mower robots, whereas the vacuum cleaners activate Bluetooth for 20 minutes upon turning on and once again during their daily reboot, making the latter somewhat more difficult to intrude.
Given that most new models of Ecovacs robots come equipped with at least one camera and a microphone, these devices can be transformed into covert surveillance tools once hijacked. Alarmingly, the robots lack any physical indicator, such as a light, to alert individuals that they are being recorded.
In some robot models, an audio notification is supposed to play every five minutes to announce camera activation, but the hackers can easily neutralize this by deleting or altering the audio file, Giese noted.
Beyond hacking concerns, Giese and Braelynn identified additional problems with Ecovacs devices, including persistent data storage on the cloud even after account deletion, plain text storage of anti-theft PINs within lawn mower devices, and the potential for one compromised robot to breach other nearby Ecovacs robots.
The list of analyzed devices includes various Ecovacs Deebot and Airbot models, heightening concerns about the widespread exploitability of these vulnerabilities.
Compiled by Techarena.au.
Fanpage: TechArena.au
Watch more about AI – Artificial Intelligence