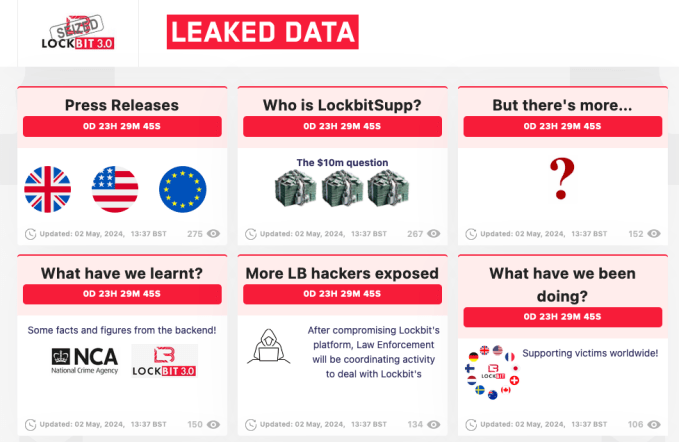
At the outset of the year, a global alliance of law enforcement agencies successfully seized the dark web portal operated by the infamous LockBit ransomware syndicate, displaying the now canonical announcement that the site was under their jurisdiction. The setback briefly hindered the group’s activities, but they quickly resurrected with a new website.
Subsequently, on the 6th of May, an intriguing update was posted on the previously captured LockBit site. The message teased the forthcoming disclosure of the identity of the administrator behind LockBit, complete with a 24-hour countdown and the question, “Who is LockBitSupp?”
The revelation caught the attention of cybersecurity expert Jon DiMaggio, who pondered if the law enforcement had identified the same individual he had.
Over the past few years, DiMaggio, an Analyst1 cybersecurity firm researcher, built a rapport with LockBitSupp by initially masquerading as an aspiring cybercriminal eager to join the group, before ultimately engaging as his true self. Eventually, DiMaggio managed to uncover LockBitSupp’s real identity before it was officially announced by authorities.
In a presentation at the Def Con hacking conference in Las Vegas, DiMaggio narrated his entire engagement with LockBitSupp. He detailed how he crafted a fictitious identity to earn the gang leader’s trust, and how he maintained their relationship even after exposing his successful penetration into the group and coaxing operation details from LockBitSupp.
“Our relationship had its highs and lows,” DiMaggio shared in an overview of his Def Con talk, which was provided to TechCrunch ahead of the event.
Initially, DiMaggio employed several sockpuppet accounts to connect with individuals believed to be directly associated with LockBitSupp, aiming to establish a credible cybercriminal profile to facilitate direct communication with LockBit and its leader.
“It was crucial to monitor those discussions that seemed insignificant, where they let their guard down, and shared candidly among themselves. Observing these moments helped me understand their preferences, dislikes, and even political leanings,” DiMaggio elucidated. “These insights were instrumental before I could initiate my approach, as jumping straight into inquiries about their operations would clearly betray my researcher’s intent.”
Despite an initial rejection, DiMaggio kept the dialogue open with LockBitSupp, transitioning to a direct and cordial exchange. He strategically inquired about the gang’s operations, probing into the nuances of their attacks and negotiation tactics with victims, without blowing his cover.
By January 2023, DiMaggio had extensively documented his undercover findings, effectively burning his cybercriminal aliases. He assumed this would spell the end of his connection with LockBitSupp. Contrary to his expectations, LockBitSupp lightly dismissed it, humorously wishing for a portrayal of high lifestyle in DiMaggio’s exposés.
“This individual, although financially motivated, does not seem enamored with material possessions in the way one might expect,” DiMaggio observed, highlighting a discrepancy between the public persona LockBitSupp projected online and their private interactions.
The rivalry turned playful when LockBitSupp started using DiMaggio’s LinkedIn picture as a profile image in hacking forums, showcasing a “cat-and-mouse” dynamic between them. “LockBit enjoyed this game just as much as I did,” DiMaggio remarked.
In a humorous twist, DiMaggio once publically baited LockBitSupp on X, jesting about imminent research that could be halted for $10 million, essentially attempting to extort the extortionists. This bluff had some criminals worried about potential exposure.
“It highlights how you can mentally manipulate these individuals,” DiMaggio noted. “The psychological strategy of this operation proved more impactful than any other action I took.”
DiMaggio recounted a moment of frustration when consecutive attacks on hospitals treating children in Chicago and Toronto’s SickKids by LockBit deeply angered him, almost prompting him to confront LockBitSupp directly. However, he refrained, emphasizing the importance of maintaining emotional detachment from the target.

After law enforcement shuttered LockBit’s website, DiMaggio shifted his focus entirely to unmasking LockBitSupp. He sought collaboration in the cybercrime world and among fellow researchers to track down the gang’s elusive leader.
“LockBit was aware that they were being hunted,” DiMaggio conveyed.
An anonymous informant then provided DiMaggio with a crucial piece of the puzzle: a Yandex email allegedly belonging to LockBitSupp. This lead allowed him to dec
ipher the mystery behind LockBitSupp’s real identity, pointing to a person named Dmitry Khoroshev. However, DiMaggio needed further confirmation of his findings.
Unexpectedly, the authorities signaled their intention to disclose LockBitSupp’s identity on the seized website. DiMaggio reached out to the FBI, a longstanding partner, to discuss whether to delay his report’s publication based on this new development. The FBI’s advice to wait confirmed DiMaggio’s suspicions about having identified the correct individual.
DiMaggio wrote his comprehensive dossier on Khoroshev while attending the RSA cybersecurity conference in San Francisco, preparing to synchronize its release with the countdown’s end. When the Department of Justice finally accused Dmitry Khoroshev of leading LockBit, DiMaggio unveiled his detailed report, including personal information and previous contact numbers,
“This marked my first experience doxing someone. And now, with his identity public, I disclosed everything I knew about him. It was challenging to resist the urge to contact him directly before the indictment, but I refrained,” DiMaggio explained.
As a farewell gesture, DiMaggio published a message to Khoroshev, reflecting on their long-standing connection and urging the cybercriminal to step away from the life of crime before it was too late.
“LockBitSupp, you’re intelligent. It’s no longer about the money for you; wanting a million victims is an ambitious goal, but it’s time to walk away. This is that moment, my old friend,” DiMaggio penned.
Since unveiling Khoroshev, DiMaggio disclosed he has not received any communication from him.
DiMaggio hopes his story will illustrate the effectiveness of immersive research in identifying cybercriminals, emphasizing the potential risks involved in such in-depth investigations. “No one emerges unharmed when delving into the world of criminals like this,” he stated.
Compiled by Techarena.au.
Fanpage: TechArena.au
Watch more about AI – Artificial Intelligence