The threat of cybercriminals targeting everyday individuals, aiming to pilfer cryptocurrency, access bank details, or simply monitor their activities, is growing. While such incidents remain uncommon, being proactive about safeguarding your personal information is crucial, particularly if a breach is suspected in your email or social networking accounts.
Years back, I drafted guidelines to assist users in bolstering their online safety. It’s worth remembering that many platforms provide security tools to help you secure your accounts even before reaching out for support, which, in some situations, is still advised.
Let’s explore several strategies for different digital services.
However, it’s crucial to acknowledge these recommended practices may not fully assure your account’s security. If uncertainties persist, seeking out a specialist is advisable, particularly for those in sensitive positions like journalists or activists, who might be more susceptible. For such cases, Access Now provides a digital security helpline.
Another valuable precaution is to enable multi-factor authentication across all key accounts such as email, banking, and social networks. This guide shows how to set up multi-factor authentication on over a thousand sites. There are several alternative apps available for this additional security measure.
Some online platforms now use a physical security key or a digital passkey in password managers as a robust defense against phishing and malware designed to steal passwords.
How to Find Active Sessions in Gmail
Upon suspicion of unauthorized Gmail access, head to the bottom of your inbox to find “Last account activity,” then click “Details.”
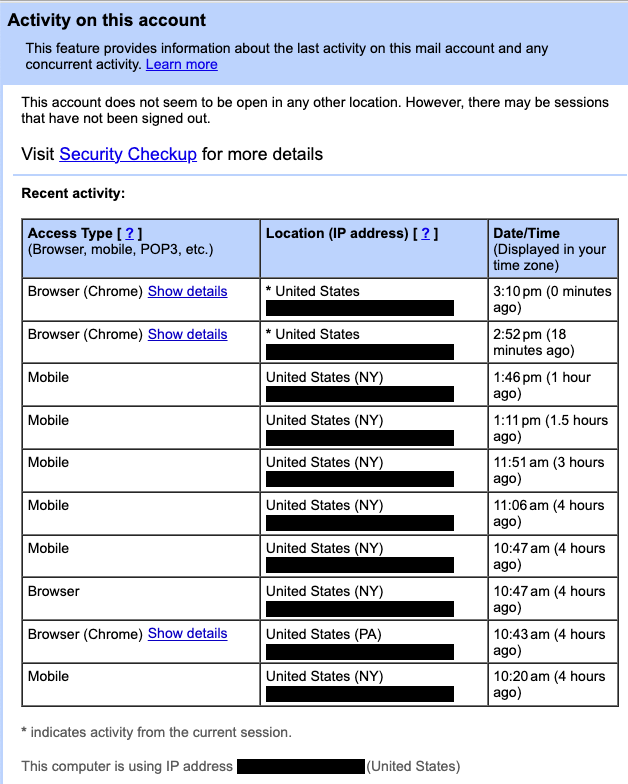
Here, you can identify all actively logged-in locations. Suspicious activities, especially those from unfamiliar places, warrant a “Security Checkup.”
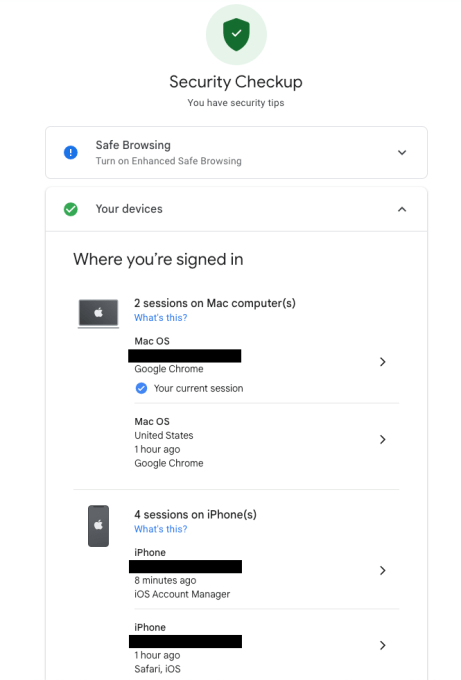
Further down, you’ll find “Recent security activity,” showing any unfamiliar devices, prompting you to update your password if needed.
Post-password change, Google clarifies you’ll be logged out from all devices except those used for identity verification and some third-party app devices. To manage these, navigate to the appropriate Google Support page.
It’s also advisable to consider Google’s Advanced Protection for users facing increased risks. This option utilizes physical security keys to toughen access control significantly.
Moreover, securing your email is paramount as it often links to your most valuable accounts, acting as a gateway for further intrusions.
Monitoring Outlook and Microsoft Account Safety
For those worried about their Microsoft Outlook account security, Microsoft provides a feature to audit your account’s sign-in history within account settings.
Yahoo offers similar tools for account and sign-in activity review, aiming to spot and mitigate unauthorized access efforts.
Safeguarding Your Apple ID
Apple furnishes direct device check-in capabilities for monitoring which devices are utilizing your Apple ID, a critical step in preemptive account safety.
Facebook and Instagram’s Account Security Features
Facebook and Instagram have streamlined security settings to manage active sessions easily. Extra protection through advanced security settings is recommended for users most vulnerable to targeted hacking attempts.
Ensuring WhatsApp Security
WhatsApp now supports multi-device usage, providing a straightforward way to observe and manage device connections for enhanced account security.
Signal’s Approach to Security
Signal ensures users can easily audit and manage connected devices, offering another layer of security for its encrypted communication service.
How to Manage Open Sessions in X (Twitter)
X provides detailed session and app connection oversight, empowering users to secure their digital presence effectively.
Compiled by Techarena.au.
Fanpage: TechArena.au
Watch more about AI – Artificial Intelligence